When I’m scrolling through social media, purchasing unnecessary items from Amazon, or googling different random thoughts - my online presence and safety aren’t two topics circling my mind. Why should it be? I generally use strong passwords and big tech platforms, so I usually assume that I’m well protected - but I definitely received a loud awakening as I dove into cybersecurity.
Two rules that become apparent:
1) Expect the unexpected
2) Nothing is impossible
The immense shift taking place between our physical and digital lives means that everything is merging into one. This may sound like a line out of a movie, but the reality is that now our digital presence can have the same if not more of an impact on our lives than we might think.
As we’ve become heavily reliant on technology within our societies, it’s clear that we need its support to function. It’s allowed us to simplify our lives - from storing sensitive information (government ids, credit cards, etc.) to all sorts of passwords for all our platforms. For large institutions, digitization of data created new levels of efficiency. Most if not all organizations store client information within a centralized database making client management much easier, so imagine if this didn’t exist?
But all this power comes great responsibility… it can all come crashing down if this private information is compromised and this is where cybersecurity comes into play.
What is Cybersecurity?
It’s the online protection applied to “internet-connected systems such as hardware, software, and data” against unauthorized access and cyber threats. This information security market is projected to be valued at $170.2 billion by 2022 and this valuation comes as no surprise with the immense rise of cyber breaches across the globe. All eyes are on the progress of this field, as the sophistication from both ends continues to rise.
Whether it’s an individual or a multi-billion dollar corporation, the objective of cyber attacks is the same. Hackers will aim to access, change, or destroy sensitive data leveraging it as ransom, identity theft, infrastructure theft or simply create chaos. The importance of cybersecurity roots from endless vulnerabilities that are possible despite the many layers of protection that can be applied - nothing becomes impossible.
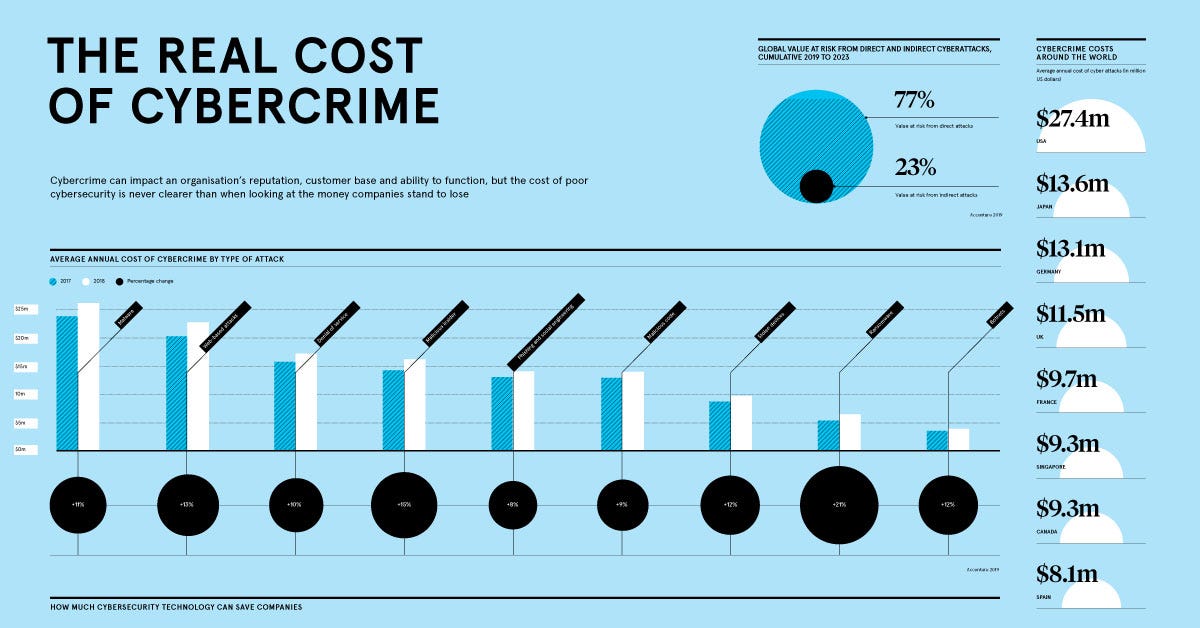
By the end of 2021, the damages of cyber crime are projected to accumulate to $6 trillion annually and up to $10.5 trillion by 2025 - representing the greatest transfer of economic wealth in history. Taking a step back, this truly puts into perspective the depth of data security and the risk that is created if cybersecurity is neglected.
On the news
Whether you’re reading this in August 2021 or August 2031, this isn’t a topic that will suddenly disappear. Lately, the news has been flooded with individuals to large corporations falling victim to cyber-attacks. Here are a few notable stories:
Schools - The education field saw an immense spike in cyber attacks recognizing its failure to adapt to the new playing field and this has greatly impacted students the most. Simon Fraser University suffered an attack exposing its own data of 200,000 students, staff, and alumni. This was only one year after the same university endured a previous attack exposing the data of 250,000 individuals.
Twitter - In the world of big tech, there are various measures in place to maneuver through any attack. However, social engineering is not so easy to get around. Attackers were able to steal employee’s credentials which gave them access to high-profile accounts including Barack Obama, Jeff Bezos, and Elon Musk. This escalated to bitcoin scams being tweeted out resulting in a loss of $100,000 for the victims.
Marriott International - A hotel chain with an enterprise value of $54.1 billion endured its second cyberattack in two years at the beginning of 2020 using employee login credentials. This attack provided access to 5.2 million guests consisting of contact details, postal codes, email addresses, and more. Despite the company’s efforts to get ahead of its 2018 data breach of 100 million guests, it proved that there were many more knots to be tied.
Is every attack the same?
As new trends and innovative technologies are introduced every year, the same can be said about the constantly adaptive attacks. Its become virtually impossible to get ahead of cyber attacks as it can come in any form and its impact can create ripples throughout an entire industry.
In the eyes of a hacker, the form of an attack can come in endless possibilities and hackers won’t be afraid to exploit any vulnerability they find. Cyber threats tend to tailor to the organization or the individual and these threats come in multiplies. It’s easy to get lost and be afraid of all the unknown but recognizing this reality is the best first step. Here are a few common cyber threats:
Malware
Ransomware
Social engineering
Phishing
Spear phishing
Distributed denial-of-service (DDoS)
Advanced persistent threats (APTs)
Man-in-the-middle (MitM) attacks
Password security will never be the same
It shouldn’t be a surprise to find out that passwords don’t truly protect you, at least not now in 2021. The root of 80% of data breaches come from compromised passwords that are cracked through brute force, social engineering, network searches and the list goes on. For nearly all platforms, passwords are a requirement, and it’s commonly suggested to create a ‘strong/long’, ‘non-predictable password that can withstand the security of various websites. When in reality, 51% of passwords are reused across all platforms proving the inefficiency that exists for account security.
And now you’re wondering, is there a solution?
Back in 2013, the FIDO (Fast Identity Online) Alliance was created among large corporations as an industry-wide association to reduce the reliance on passwords and defer to multi-factor authentication and public-key cryptography. FIDO replaces password databases with personally identifying information (PII) opening new doors for authentication use cases:
Passwordless authentication
Second-factor authentication (i.e. using a security key)
Biometric/Multi-factor authentication (i.e. facial recognition, fingerprint, voice)
Its long-term objective is to standardize new layers of privacy and security measures using FIDO2 and Universal Second Factor (U2F) authentications. With recognition to this innovative authentication system and its potential, large corporations including Apple, Facebook, Google, Microsoft, and many others have joined the alliance.
Who are the players in the game?
Cisco Systems - The global leading hardware and software supplier in networking solutions. As the largest public cybersecurity company with an enterprise value of $221.29 billion, the company holds various platforms to provide a wide array of solutions for software-defined security, firewall software, software networking, analytics, and intent-based networking. Cisco’s subscription and recurring sales revenue model continue to supports its long-term to vision to lead this industry.
Valuation: $221.29 billion
Tanium - This endpoint management and security platform provide precision data to enable and strengthen clients through critical IT decisions. The company leverages high-fidelity data to regain control/visibility of threats and better understand the scope of its environment. It was founded back in 2007 and has raised a total of $982.79 million as it continued to gain momentum.
Valuation: $9 billion
Notable Investors: ADS Ventures, Fabrica Ventures, Salesforce Ventures, and Andreessen Horowitz.
1Password - Toronto-based password management software enables clients to save and remember passwords. The platform provides a user-friendly experience to create and maintain strong credentials, manage access and ensure privacy to prevent data breaches. The differentiating factor among its competitors is its exclusive usage of vaults treated as an additional layer of protection to access passwords. To date, it’s raised a total of $300.14 million.
Valuation: $2 billion
Notable Investors: Accel, Skip Capital, Slack Fund, and Sound Ventures.